Saturday, March 15, 2014
SIM Test Card Hardware Layouts
15/11/97
Interface for ASIM
README This file.
EMUSIM.BMP Artwork of Smart Card sized PCB
MAX232.BMP Artwork of Smart Card sized PCB whith MAX232
MAX232LY.GIF Parts placement guide of max232 pcb.
CIRCLAY.GIF Parts placement guide.
The bitmap file can be loaded into Windows Paintbrush then printed. They
are drawn 1:1 at 300 dpi so make sure you click "Use printer resolution" and
the Laser printer is set to 300 dpi before you print. The artwork is drawn as
seen from the copper side. It can be printed on a transparency as is and used
directly in a positive photo etch. The copper side of PCB not touches the
toner side of transparency.
Bye
by Giulio Cesare
Sunday, October 06, 2013
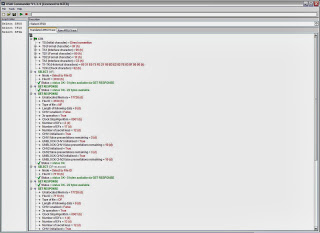
(U)ICC/(U)SIM Script Commands and Responses
GSM ICC/SIM script selecting Master File, Dedicated File and Elementary File
Reason for script test : defining an examination procedure to isolate and test a single elementary file; determine the EF's status, file structure, coding etc; conrroborate the ability of the (U)ICC/(U)SIM to action responses from commands sent to card; provide corroborating evidence of commands sent to the card to demonstrate evidential integrity (transparency of practices and procedures); testing the examination card reader is functioning correctly; QA procedures.
Script examination tool used : USIM Commander - http://www.quantaq.com/usimcommander.htm
Relevant Core Diplomas:-
Aims : MTEB Diploma for Mobile Evidence QA and Evidence Handling - Mobile Telephone Diploma Core CQAE1
Objectives : Device Maintenance and Calibration; Examination Procedure
Aims : MTEB Diploma for SIM and USIM Technology Examination - Mobile Telephone
Diploma Core CSUT2
Objectives : Your understanding of roles and responsibilities and the importance of
appropriate practices and procedures for SIM and USIM Technology
Examination for acquiring evidence.
Reference Standards :
GSM11.11/3GPP TS51.011/3GPP TS31.102,
GSM11.12,
GSM11.17/3GPP TS51.017/3GPP TS31.120/3GPP TS31.121/3GPP TS31.122,
GSM11.18/3GPP31.101,
EU MTEB Diploma Student Note : Remember to check with ETSI Standards e.g. TS102.221 etc
US MTEB Diploma Student Note : Diploma Students remember to check e.g. C.S0065-0 v1.0, C.S0074-0 v1.0, C.S0074-A v1.0, N.S0009-0 v1.0, S.R0095-0 v1.0 etc
Generically speaking, apart from GSMA and 3GPP, there is also 3GPP2 which also includes ARIB, CCSA, TIA TTA, TTC that all have conditions that can impact/influence results on (U)ICC/(U)SIM.
The discussion under (U)ICC/(U)SIM Script Commands and Responses is one of a number that will appear here to assist Diploma students with their course work.
The latest MTEB Diploma Modules Guide MTEdipl 2.2 can be downloaded here:
https://dl.dropboxusercontent.com/u/84491783/MTEdipl%202.2.pdf
Saturday, September 14, 2013
Blocked SIM
For a quick solution it is best to go to the operator to obtain a PUK code where there has been 3 CHV1 attempts and access is now blocked.
If it is 10 CHV1 attempts and blocked ([unless you know and have the test tools to e.g. slow the card]) then the operator may request that you send it to them and they in turn (depending upon their security level) may need to send it to the (U)ICC producer / manufacturer.
Today's UICC (using improved silicon and security techniques) have significant security improvements within each operator's card where there are various levels of electronic counter-measures (traps doors/dead-man's trap etc). Many of us (including me) simply cannot access certain areas of the UICC unless a flaw in the security is discovered. Unless you are confident of what you know and what you are doing, my observation is take the safest route.
None of the opinions I express originate based upon my gut feeling about a particular matter. I research, like others, to establish the industry security protocols, practices and procedures and then consider the position from there. It is important to bare in mind that forensics and evidence is not about hacking everything in sight or writing a program to extract data but to be aware and comprehend how industry standard bodies intended security should be implement, which norms the manufacturer and operator follow and whether following implementation security flaws occur.
(U)SIM Examination (Physical) Pt2
Before we can progress to consider various methods of (U)SIM physical examination there are more standards we need to be aware and there are reasons for that. Transitioning from GSM to 3GPP (*wcdma) standards required rewriting existing GSM standards to make the standards technology neutral to integrate GSM into future mobile developments under 3GPP global standards. Technology-wise, we know that GSM is a defined circuit-switched voice mobile communications system that has evolved with value-added data services (GPRS, HSCSD and EDGE). 3GPP (wcdma) as we know is a defined packet-switched technology and thus would be a pointless exercise to re-invent the wheel, so to speak, and introduce a new voice circuit-switched system and the matured installation base that went with it. That needs to be understood on many levels when dealing with mobile communications. Three examples of GSM and 3GPP working together:
(i) generally, we refer to Release 99 (R99) as a reference point whereby 3GPP could transition and re-write mobile communication technology standards with birthing-periods: GSM only before 3GPP Release 4 (Rel-4); GSM only (Rel-4 and later); 3GPP and beyond / GSM (R99 and later). This enabled manufacturers, developers and operators and service providers to conintue with GSM standards in a pure GSM environment or evolve to a 3GPP environment but in the knowledge access and inter-connectivity to GSM would continue:
(ii) introduction of 3GPP (*wcdma) would take time and thus should avoid, as best possible, disruption to existing moble services;
(iii) GSM user/subscriber base was still growing at that time and has now reached over 3-billion users, from which we can draw a conclusion that GSM's importance in its relationship with 3GPP should not be under-estimated.GSM is by no means the junior partner.
In the mobile examination environment, we, as examiners, are exposed to multitude and multiple-layers of technical and technology standards many of which impact on (U)SIM, and particuarly so if the technical and technology generates a mobile communication outcome associated to/with a user/subscriber.
(*) wcdma is one of a family of mobile technology standards under 3GPP and has been used for easy of reference.
The scope of the tests and the requirements set down in GSM1117 were reproduced under the approved and adopted standard 3GPP TS51.017. In Pt1( usim-examination-physical-pt1.html ) reference was made to GSM11.11, however the approved and adopted standard (and the counterpart to GSM11.11) is 3GPP TS51.011:
PHY: Physical characteristics - 3GPP TS 51.011 [1], clause 4.
ELEC: Electronic signals and transmission protocols - 3GPP TS 51.011 [1], clause 5.
AFS: Application and File structure - 3GPP TS 51.011 [1], clause 6.
SEC: Security features - 3GPP TS 51.011 [1], clause 7.
CMD: Description of the commands - 3GPP TS 51.011 [1], clause 9.
CEF: Contents of the elementary files - 3GPP TS 51.011 [1], clause 10.
APP: Application Protocol - 3GPP TS 51.011 [1], clause 11.
Whilst GSM11.17 standard is the starting point for ICC/SIM and 3GPP TS51.011 moved the technology to neutral ground to enable 3GPP to evolve 3G environment standards incorportating interconnectivity to and backward compatibility for ICC/UICC, the 3GPP evolution hasn't stopped there. There is, of course, 3GPP TS 31.120 the aim of which is to ensure interoperability between an UICC and a Terminal independently of the respective manufacturer, card issuer or operator. This is the expansion of the 3GPP domain going beyond specific limitations encumbent with a particular proprietory technology.
The run of standards doesn't end there. Attention and consideration should be given to:
ETSI standards
TS 102 230
TS 102 221
International standards
ISO/IEC 7816-pt1 to pt4
The standards referred to above are merely a starting point to identify the complexities involved in dealing with (U)SIM card and tasks involved in considering examination techniques that may not simply relate to recovery of data but other aspects and attributes of a card which may point to evidence. Readers should be prepared to delve into the standards above and release the huge number that haven't been mentioned. There are various analogies that may be used to imagine what I have in mind for this physical series, but I quite like the analogy about forensic vehicle tyre analysis. Evidentially, consideration is given to tyre size, tread, pressure, rubber, moulding, any wheel balacing and so on to assess a skid mark or tracks at the scene of a crime. It is equally possible to use an investigative and examination approach to SIM/USIM card materials, contacts, gold content, embossing etc to identify potential evidence.
Monday, May 30, 2011
Answer To Reset (ATR)
It is an endless investigation when dealing with SIM/USIM. The intention of this discussion is to highlight discoveries that you may not be aware. In this instance ATR is the first data read from every SIM/USIM and can provide potentially useful information to an investigation or when making analysis about end-to-end (SIM to Network) mobile telephone evidence.
What might be interpreted from first eight bytes of an ATR recovered? From research, this is an interpretation of the ATR from a particular manufacturer's GSM SIM:
[B1][B2][B3][B4][B5][B6][B7][B8]
3B....34...11...00...6B...C?..16...0?
Byte 6 - options
3B 34 11 00 6B C2 16 0? normal SIM+OTA
3B 34 11 00 6B C3 16 0? SIM-Toolkit (STK) SIM
Byte 7
16 EEPROM size (16K)
Byte 8 - options
3B 34 11 00 6B C? 16 01 GSM security algorithm
3B 34 11 00 6B C? 16 02
3B 34 11 00 6B C? 16 03
3B 34 11 00 6B C? 16 0A
Wednesday, November 03, 2010
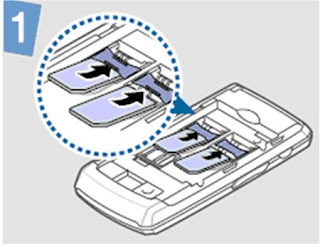
Quad-SIM (4 in 1)
Wonder how we will handle the examination of this beast? Which profile will need to be read first? Will the handset have different profiles? Will each SIM have its own password? There are so many question this news story raises. Previous experience has shown care is needed with handling the examination of handsets containing two (dual) SIMs (http://sim2usim.blogspot.com/2008/11/cloning-test-sim-cards.html).
Spreadtrum Announces the World’s First Single Chip Quad-SIM Standby Solution
The SC6600L6 allows four GSM SIM cards simultaneously running on standby mode with only one set of baseband and RF. It integrates a processor engine and controller for supporting quadruple SIM cards and has an improved graphic user interface for Quad-SIM. The product supports different multi-SIM options, including dual SIM, triple SIM, and Quad-SIM in a single set of baseband and RF chip, provides more choices to handset designers and meets need of users from different regions.
http://www.spreadtrum.com/eng/showNews.asp?name=1&ID=306
Tuesday, November 02, 2010
Smart Card Hacking
Back in 2002 I wrote about SIM Card Cloning for examiners to demonstrate the state of the market place, where software and hardware was being openly promoted that researchers could obtain and what might an examiner be exposed to when examining a cloned SIM Card. A copy of that report can be downloaded here:
SIM Card Cloning
http://www.4shared.com/document/GMz_Gqcc/Special_Edition_2002_SIM_Cloni.html
In 1998 I circulated a report (UPD5-1 Vol1 - FEN98) on Smart Card Hacking to members of the British Association of Criminal Experts (BACE). The archive report has been scanned page by page and put into acrobat.pdf format and can now be downloaded here:
Smart Card Hacking
http://www.4shared.com/file/kq5NGzns/UPD5-1_Vol1_-_FEN98.html
The smart card hacking report has an interesting description for classification of the various levels of criminal activity in addition to techniques of smart card hacking. This particular report was the one that inspired me to write about SIM Card Cloning for exmainers. Once again thanks and respect to Ross Anderson and Markus Kuhn.
It is important to consult the laws of the country you are in when dealing with research for cloning SIM Cards. This blog article does not promote or advocate anyone to break the law by cloning or attempting to clone SIM cards for the purposes of obtaining services or breaching property rights belonging to respective particular network operators etc.
Monday, June 21, 2010
3G USIM 2G SIM Service Numbers
3G USIM (2010-04)
Service n°1: Local Phone Book
Service n°2: Fixed Dialling Numbers (FDN)
Service n°3: Extension 2
Service n°4: Service Dialling Numbers (SDN)
Service n°5: Extension3
Service n°6: Barred Dialling Numbers (BDN)
Service n°7: Extension4
Service n°8: Outgoing Call Information (OCI and OCT)
Service n°9: Incoming Call Information (ICI and ICT)
Service n°10: Short Message Storage (SMS)
Service n°11: Short Message Status Reports (SMSR)
Service n°12: Short Message Service Parameters (SMSP)
Service n°13: Advice of Charge (AoC)
Service n°14: Capability Configuration Parameters 2 (CCP2)
Service n°15: Cell Broadcast Message Identifier
Service n°16: Cell Broadcast Message Identifier Ranges
Service n°17: Group Identifier Level 1
Service n°18: Group Identifier Level 2
Service n°19: Service Provider Name
Service n°20: User controlled PLMN selector with Access Technology
Service n°21: MSISDN
Service n°22: Image (IMG)
Service n°23: Support of Localised Service Areas (SoLSA)
Service n°24: Enhanced Multi Level Precedence and Pre emption Service
Service n°25: Automatic Answer for eMLPP
Service n°26: RFU
Service n°27: GSM Access
Service n°28: Data download via SMS-PP
Service n°29: Data download via SMS CB
Service n°30: Call Control by USIM
Service n°31: MO-SMS Control by USIM
Service n°32: RUN AT COMMAND command
Service n°33: shall be set to '1'
Service n°34: Enabled Services Table
Service n°35: APN Control List (ACL)
Service n°36: Depersonalisation Control Keys
Service n°37: Co-operative Network List
Service n°38: GSM security context
Service n°39: CPBCCH Information
Service n°40: Investigation Scan
Service n°41: MExE
Service n°42: Operator controlled PLMN selector with Access Technology
Service n°43: HPLMN selector with Access Technology
Service n°44: Extension 5
Service n°45: PLMN Network Name
Service n°46: Operator PLMN List
Service n°47: Mailbox Dialling Numbers
Service n°48: Message Waiting Indication Status
Service n°49: Call Forwarding Indication Status
Service n°50: Reserved and shall be ignored
Service n°51: Service Provider Display Information
Service n°52 Multimedia Messaging Service (MMS)
Service n°53 Extension 8
Service n°54 Call control on GPRS by USIM
Service n°55 MMS User Connectivity Parameters
Service n°56 Network's indication of alerting in the MS (NIA)
Service n°57 VGCS Group Identifier List (EFVGCS and EFVGCSS)
Service n°58 VBS Group Identifier List (EFVBS and EFVBSS)
Service n°59 Pseudonym
Service n°60 User Controlled PLMN selector for I-WLAN access
Service n°61 Operator Controlled PLMN selector for I-WLAN access
Service n°62 User controlled WSID list
Service n°63 Operator controlled WSID list
Service n°64 VGCS security
Service n°65 VBS security
Service n°66 WLAN Reauthentication Identity
Service n°67 Multimedia Messages Storage
Service n°68 Generic Bootstrapping Architecture (GBA)
Service n°69 MBMS security
Service n°70 Data download via USSD and USSD application mode
Service n°71 Equivalent HPLMN
Service n°72 Additional TERMINAL PROFILE after UICC activation
Service n°73 Equivalent HPLMN Presentation Indication
Service n°74 Last RPLMN Selection Indication
Service n°75 OMA BCAST Smart Card Profile
Service n°76 GBA-based Local Key Establishment Mechanism
Service n°77 Terminal Applications
Service n°78 Service Provider Name Icon
Service n°79 PLMN Network Name Icon
Service n°80 Connectivity Parameters for USIM IP connections
Service n°81 Home I-WLAN Specific Identifier List
Service n°82 I-WLAN Equivalent HPLMN Presentation Indication
Service n°83 I-WLAN HPLMN Priority Indication
Service n°84 I-WLAN Last Registered PLMN
Service n°85 EPS Mobility Management Information
Service n°86 Allowed CSG Lists and corresponding indications
Service n°87 Call control on EPS PDN connection by USIM
Service n°88 HPLMN Direct Access
Service n°89 eCall Data
Service n°90 Operator CSG Lists and corresponding indications
------------------------------------------------------------------
2G SIM (2007-06)
Service n°1 : CHV1 disable function
Service n°2 : Abbreviated Dialling Numbers (ADN)
Service n°3 : Fixed Dialling Numbers (FDN)
Service n°4 : Short Message Storage (SMS)
Service n°5 : Advice of Charge (AoC)
Service n°6 : Capability Configuration Parameters (CCP)
Service n°7 : PLMN selector
Service n°8 : RFU
Service n°9 : MSISDN
Service n°10: Extension1
Service n°11: Extension2
Service n°12: SMS Parameters
Service n°13: Last Number Dialled (LND)
Service n°14: Cell Broadcast Message Identifier
Service n°15: Group Identifier Level 1
Service n°16: Group Identifier Level 2
Service n°17: Service Provider Name
Service n°18: Service Dialling Numbers (SDN)
Service n°19: Extension3
Service n°20: RFU
Service n°21: VGCS Group Identifier List (EFVGCS and EFVGCSS)
Service n°22: VBS Group Identifier List (EFVBS and EFVBSS)
Service n°23: enhanced Multi-Level Precedence and Pre-emption Service
Service n°24: Automatic Answer for eMLPP
Service n°25: Data download via SMS-CB
Service n°26: Data download via SMS-PP
Service n°27: Menu selection
Service n°28: Call control
Service n°29: Proactive SIM
Service n°30: Cell Broadcast Message Identifier Ranges
Service n°31: Barred Dialling Numbers (BDN)
Service n°32: Extension4
Service n°33: De-personalization Control Keys
Service n°34: Co-operative Network List
Service n°35: Short Message Status Reports
Service n°36: Network's indication of alerting in the MS
Service n°37: Mobile Originated Short Message control by SIM
Service n°38: GPRS
Service n°39: Image (IMG)
Service n°40: SoLSA (Support of Local Service Area)
Service n°41: USSD string data object supported in Call Control
Service n°42: RUN AT COMMAND command
Service n°43: User controlled PLMN Selector with Access Technology
Service n 44: Operator controlled PLMN Selector with Access Technology
Service n 45 HPLMN Selector with Access Technology
Service n 46: CPBCCH Information
Service n 47: Investigation Scan
Service n°48: Extended Capability Configuration Parameters
Service n°49: MExE
Service n°50 Reserved and shall be ignored
Saturday, June 05, 2010
MTEdipl Diplomas
.
Three Months Notice (June/July/August) Advanced reading to help you prepare for the distance learning and self study. The following book comes highly recommended and will help you with setting your objectives particularly for the research and study modules for each Diploma.
.
LITERATURE:
Skills for Success, The Personal Development Planning Handbook
Author: Stella Cottrell Paperback: 312 pages
Publisher: Palgrave Macmillan (2 May 2003)
Language English ISBN-10: 1403911320
.
Amazon link:
http://www.amazon.co.uk/Skills-Success-Personal-Development-Planning/dp/1403911320
Tuesday, May 25, 2010
Diplomas: MTEdipl Syllabus and Student Handbook
The distance learning and self-study Diplomas: Mobile Telephone Evidence (MTEdipl) Syllabus and Student Handbook is now available for download:
http://www.4shared.com/document/7XHHJ1Ru/MTEdipl_Cata20.html
Friday, May 15, 2009
Undercover Officer Down, how might SIM Access Control Class help? Part 1
Monday, February 02, 2009
SIM PIN Challenge 2
A reminder that this challenge ends on the 15th February 2009:
.
http://trewmte.blogspot.com/2009/01/sim-pin-challenge.html
.
No pressure here guys, but we have had the first written response to the SIM PIN Challenge from a Challenge Entrant who has just started in mobile telephone forensics. This Challenge should therefore be a walk in the park for all you mobile phone and computer forensic examiners who have given evidence about SIM Cards in Court.
.
As a brief history about SIM Cards, the requirement for *Personal Identity Number (PIN) to be available in a SIM Card is defined by way of the GSM Standard GSM11.11. Moreover, GSM11.11 v3 1995 standard and onwards can be downloaded free of charge. So at least we know there is over 13 years of technical knowledge about SIM Card PIN that is traceable. Furthermore, there are other standards that are used to test for allocation and activation of PIN and the mandated execution of the function between the mobile phone and SIM Card.
.
*Do remember that PIN is only used because it is comon language now, but has been made obsolete from the standards and replaced by CHV (Card Holder Verification).
.
Finally, many ten of thousands of SIM Cards have been examined and their evidence, along with examiners' testimonies/experts' opinions, have been presented in criminal proceedings at Court for well over a decade. A large number of the SIM Cards presented for examination had PIN enabled, thus understanding the fundamental operation of PIN is vital to forensic investigation understanding and the evidence presented about it.
.
I have sent copies of this Challenge and MOBILE FORENSICS AND EVIDENCE DEGREES/CHALLENGE (see weblink at the end of this discussion) to the following who have the responsibility for: innovation, universities and skills; and regulation of forensic sciences:
.
MOBILE FORENSICS AND EVIDENCE DEGREES/CHALLENGE
Thursday, January 08, 2009
SIM PIN Challenge
 .
.So does that mean a particular EF under the MF in SIM with a logical address 3F00 0000 is always going to be the CHV1 file and would the raw data from that EF reveal a user's PIN number?
.
Below are raw data extracts from three phases of SIM cards - Phase 1, Phase 2 and Phase 3 (2+) and harvested from the Master File (MF) 3F00 and an unnamed EF immediately under the MF with an address 3F00 0000.
.
Your challenge, if you are interested, is to examine the raw data and corroborate whether the data reveals a user's CHV1 (PIN number) or not.
.
To help, you may want to check the GSM SIM card standard GSM 11.11 to comprehend file structure, formatting and coding etc for elementary files and to learn what the standard has to say about CHV/PIN.
.
As forensic investigators you shouldn't need the 'carrot and stick' approach to get you to undertake this challenge because I know how much you all love your work and can't get enough of it and that should be reward enough :-). However, the first person who posts the correct answer at Forensic Focus , I am sure we can sort out some sort of prize:
.
http://www.forensicfocus.com/index.php?name=Forums&file=viewtopic&t=3349
.
However, there are some rules (there is always something like this):
.
1) In your answer it should contain identification to a document or weblink that supports the answer (the document/weblink must be traceable and not based on "something somebody told you"). This will be checked before any prize is awarded.
2) Challenge closes 15th February 2009.
3) I wont be giving the answer, because I do not want everyone just to sit back and think they can wait for my reply.
.
GOOD LUCK
.
PHASE 1 SIM Card
3F00
--------------------------------------------------------------------------------
Response: 00 00 1A 47 3F 00 00 00 F1 F4 44 13 15 83 02 03 04 00 82 8A 00 00 00 00 00 00 00 00 00 00 00 00 00 00
----------------------------------------
Allocated memory :1A47File ID :3F00
Type of file :MFNumber of DF : 2
Number of EF : 3 Number of CHV's : 4
CHV1(PIN1) :Disabled
CHV1(PIN1) Status :2 Tries left
CHV1(PIN1) Status :10 Tries left
CHV1(PIN1) Status :0 Tries left
CHV1(PIN1) Status :0 Tries left
--------------------------------------------------------------------------------
.
3F00:0000
--------------------------------------------------------------------------------
Response: 00 00 00 18 00 00 00 00 FF FF FF 13 06 00 00 02 01 00 00 0A FF
----------------------------------------
File ID :0000
Type of file :RFU
Structure of file :Transparent
File Size :0018
Read Access :CHV (PIN) 15
Write Access :CHV (PIN) 15
Increase Access :CHV (PIN) 15
Rehabilitate :CHV (PIN) 15
Invalidate Access :CHV (PIN) 15
File Status :Not Invalidated
--------------------------------------------------------------------------------
.
Phase 2 SIM Card
3F00
--------------------------------------------------------------------------------
Response: 00 00 63 9C 3F 00 01 FF FF FF FF 01 0E 93 02 07 02 00 83 8A 00 00 00 00 83 00 FF
----------------------------------------
Allocated memory :639C
File ID :3F00
Type of file :MF
Number of DF : 2
Number of EF : 7
Number of CHV's : 2
CHV1(PIN1) :Disabled
CHV1(PIN1) Status :3 Tries left
CHV1(PIN1) Status :10 Tries left
CHV1(PIN1) Status :0 Tries left
CHV1(PIN1) Status :0 Tries left
--------------------------------------------------------------------------------
.
3F00:0000
--------------------------------------------------------------------------------
Response: 00 00 00 12 00 00 04 00 FA FF FF 01 02 00 00
----------------------------------------
File ID :0000
Type of file :EF
Structure of file :Transparent
File Size :0012
Read Access :CHV (PIN) 15
Write Access :CHV (PIN) 10
Increase Access :CHV (PIN) 15
Rehabilitate :CHV (PIN) 15
Invalidate Access :CHV (PIN) 15
File Status :Not Invalidated
--------------------------------------------------------------------------------
.
Phase 3 (2+) SIM Card
3F00
--------------------------------------------------------------------------------
Response: 00 00 00 01 3F 00 01 00 00 00 00 00 09 81 04 12 0A 00 83 8A 83 8A
----------------------------------------
Allocated memory :0001
File ID :3F00
Type of file :MF
Number of DF : 4
Number of EF : 18
Number of CHV's : 10
CHV1(PIN1) :Disabled
CHV1(PIN1) Status :3 Tries left
CHV1(PIN1) Status :10 Tries left
CHV1(PIN1) Status :3 Tries left
CHV1(PIN1) Status :10 Tries left
--------------------------------------------------------------------------------
.
3F00:0000
--------------------------------------------------------------------------------
Response: 00 00 00 17 00 00 04 00 FB FF FF 01 02 00 00
----------------------------------------
File ID :0000
Type of file :EF
Structure of file :Transparent
File Size :0017
Read Access :CHV (PIN) 15
Write Access :CHV (PIN) 11
Increase Access :CHV (PIN) 15
Rehabilitate :CHV (PIN) 15
Invalidate Access :CHV (PIN) 15
File Status :Not Invalidated
--------------------------------------------------------------------------------
Saturday, November 01, 2008
Cloning Test SIM Cards
Cloning test SIM cards can present problems if their use is not carefully monitored and can lead to loss of data from a device under test (DUT). There appears many different instances under which the loss of data can occur when using a cloning test SIM card. Some examples are:
.
- The inadequate level of notice and advice within the applications that create the clone test SIM card to precisely define that a particular Make/Model of handset has been tested using the cloning application before using with a partricular Make/Model or where the guide generally infers the application is usable with a particular Make.
.
- Whether the cloned test SIM card has been correctly recorded or not, before inserting it into the device under examination (DUT).
.
- The 'trial and error' approach being applied to evidential mobile phones leading to loss of data, where the written advice in the guide, when given, doesn't deal with the examination problem at hand.
.
Taking one example of a mobile phone examination problem relating to the Samsung D880.
.

This mobile phone is capable of having two SIM cards inserted, at the same time, in order to allow for two different subscriber accounts to be used separately by a user. To understand the difference compare the position when dealing with the traditional way of having to manually swop a SIM card with another in a device that is a single-inserted SIM card operating mobile phone.
.
Once the user has selected to use one of the two SIM Cards inserted, the option to switch to a particular SIM in normal user mode is via the 'SIM selection key' with visual Icons displayed on the device's screen confirming which SIM and subscription account is in use.

1) Take out one of the user SIM cards and produce a cloned test SIM card, whilst leaving the other user SIM card in place? Then insert the new clone test SIM card and then examine the phone? It is unlikely this could work well because an original user SIM card is still in place, thus the mobile phone could still register to the network etc. That is so, because the examiner doesn't know which SIM and subscription account was last used by the mobile phone. The notion of switching the mobile phone 'ON' prior to using a cloned Test SIM card to find out begs the question why is the examiner using cloned test SIM cards in the first place?
2) Take out both user SIM cards and produce two cloned test SIM cards, but insert only one test card and examine on that basis? This might work, provided of course the examiner has selected for access the right SIM slot and subscription account, which is a bit 'trial and error', 'hit and miss'? Moreover, assuming the above method had worked and the examiner safely selected the correct SIM slot/account - for example by taking the pragmatic step of recording which user SIM came out of which slot and replacing the correct cloned test SIM card into the slot - what happens when the second cloned test SIM card needs to be inserted? Using the SIM selection key to switch to another SIM card may not assist because there isn't a cloned test SIM card in the second slot for the device to read any details. Moreover, bearing in mind the device memory has noted only one SIM inserted the first time around what impact might now happen if a second cloned test SIM card is inserted? Will it allow access to the subscriber account user data on the device? Furthermore, what happens when switching over to the other cloned test SIM card?
3) Inevitably, the line of reasoning in this discussion is intended to bring the reader's attention to the option of putting both cloned test SIM cards into the appropriate SIM slots and examining further from that standpoint. But what happens then if the device does not give up its riches and enables the examiner to gain access to the user data? Turning to the cloned test SIM cards guides, what if they provide no assistance at all? What if the cloning application may not record properly to the cloned test SIM card or the data that it does record are insufficient for a particular make and model of mobile phone to function in the way it is expected?
.
In each of the above cases where loss of data might occur, that is to say e.g. where no call history or text messages are accesible, it may not be because the user has deleted them or the user has gone to settings to set a calendar event to delete texts or clear call history on a date and time, but may be because the cloned test SIM card may have removed access to them and the examiner may not be aware of that until either using a device reading program or conducting manual examination.
.
The presumption suggested that the examination and the tools used to recover data from a device were functioning properly and without flaw at the time of the examination arising from the mobile phone data being served in evidence, inferring that it is safe to rely on, may not meet the maxim omnia praesumuntur rite esse acta, as expressed by Lord Griffiths in the case of R .v. Shepherd [1993] AC380. That can be so because it has never simply been solely about whether the original device (exhibit) was working properly at the material time, but of equal significance whether in the obtaining and the processes used to obtain data that the evidence is safe to rely on. The latter requirement did not disappear in the wake of the repeal of section 69 Police and Criminal Evidence Act 1984. Nor did it disappear by the introduction of the Criminal Procedures and Investigations Act 1996, The Police Act 1997, The Regulation of Investigatory Powers Act 2000 and so on.
.
The purpose of raising this discussion (for examiners and students) about mobile phone forensic examination and tools it that discussions on these types of topics are not simply about providing answers and solutions to problems, but identifying potential questions that need to be adddressed before using cloned test SIM cards.
.
Lastly, I have not described every event dealing with the examination of a dual SIM card mobile phone or how Samsung D880 manages the operation and functionality of both SIM cards. By not referring to these matters it has helped simplify and refine the discussion to keep the important points to the fore.