Cloning Test SIM Cards
.Cloning test SIM cards can present problems if their use is not carefully monitored and can lead to loss of data from a device under test (DUT). There appears many different instances under which the loss of data can occur when using a cloning test SIM card. Some examples are: .
- The inadequate level of notice and advice within the applications that create the clone test SIM card to precisely define that a particular Make/Model of handset has been tested using the cloning application before using with a partricular Make/Model or where the guide generally infers the application is usable with a particular Make..
- Whether the cloned test SIM card has been correctly recorded or not, before inserting it into the device under examination (DUT)..
- The 'trial and error' approach being applied to evidential mobile phones leading to loss of data, where the written advice in the guide, when given, doesn't deal with the examination problem at hand..
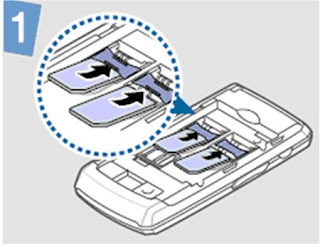
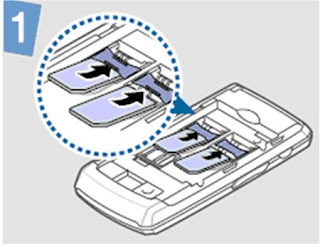
Taking one example of a mobile phone examination problem relating to the Samsung D880..
 .
.
This mobile phone is capable of having two SIM cards inserted, at the same time, in order to allow for two different subscriber accounts to be used separately by a user. To understand the difference compare the position when dealing with the traditional way of having to manually swop a SIM card with another in a device that is a single-inserted SIM card operating mobile phone.
. 
Once the user has selected to use one of the two SIM Cards inserted, the option to switch to a particular SIM in normal user mode is via the 'SIM selection key' with visual Icons displayed on the device's screen confirming which SIM and subscription account is in use.
 Problematical for the examiner using cloned test SIM cards is what is the safest method for examining a dual SIM card mobile phone. Looking at some options, what problems can arise for the examiner:
Problematical for the examiner using cloned test SIM cards is what is the safest method for examining a dual SIM card mobile phone. Looking at some options, what problems can arise for the examiner:
1) Take out one of the user SIM cards and produce a cloned test SIM card, whilst leaving the other user SIM card in place? Then insert the new clone test SIM card and then examine the phone? It is unlikely this could work well because an original user SIM card is still in place, thus the mobile phone could still register to the network etc. That is so, because the examiner doesn't know which SIM and subscription account was last used by the mobile phone. The notion of switching the mobile phone 'ON' prior to using a cloned Test SIM card to find out begs the question why is the examiner using cloned test SIM cards in the first place?
2) Take out both user SIM cards and produce two cloned test SIM cards, but insert only one test card and examine on that basis? This might work, provided of course the examiner has selected for access the right SIM slot and subscription account, which is a bit 'trial and error', 'hit and miss'? Moreover, assuming the above method had worked and the examiner safely selected the correct SIM slot/account - for example by taking the pragmatic step of recording which user SIM came out of which slot and replacing the correct cloned test SIM card into the slot - what happens when the second cloned test SIM card needs to be inserted? Using the SIM selection key to switch to another SIM card may not assist because there isn't a cloned test SIM card in the second slot for the device to read any details. Moreover, bearing in mind the device memory has noted only one SIM inserted the first time around what impact might now happen if a second cloned test SIM card is inserted? Will it allow access to the subscriber account user data on the device? Furthermore, what happens when switching over to the other cloned test SIM card?
 3) Inevitably, the line of reasoning in this discussion is intended to bring the reader's attention to the option of putting both cloned test SIM cards into the appropriate SIM slots and examining further from that standpoint. But what happens then if the device does not give up its riches and enables the examiner to gain access to the user data? Turning to the cloned test SIM cards guides, what if they provide no assistance at all? What if the cloning application may not record properly to the cloned test SIM card or the data that it does record are insufficient for a particular make and model of mobile phone to function in the way it is expected?.
3) Inevitably, the line of reasoning in this discussion is intended to bring the reader's attention to the option of putting both cloned test SIM cards into the appropriate SIM slots and examining further from that standpoint. But what happens then if the device does not give up its riches and enables the examiner to gain access to the user data? Turning to the cloned test SIM cards guides, what if they provide no assistance at all? What if the cloning application may not record properly to the cloned test SIM card or the data that it does record are insufficient for a particular make and model of mobile phone to function in the way it is expected?.
In each of the above cases where loss of data might occur, that is to say e.g. where no call history or text messages are accesible, it may not be because the user has deleted them or the user has gone to settings to set a calendar event to delete texts or clear call history on a date and time, but may be because the cloned test SIM card may have removed access to them and the examiner may not be aware of that until either using a device reading program or conducting manual examination..
The presumption suggested that the examination and the tools used to recover data from a device were functioning properly and without flaw at the time of the examination arising from the mobile phone data being served in evidence, inferring that it is safe to rely on, may not meet the maxim omnia praesumuntur rite esse acta, as expressed by Lord Griffiths in the case of R .v. Shepherd [1993] AC380. That can be so because it has never simply been solely about whether the original device (exhibit) was working properly at the material time, but of equal significance whether in the obtaining and the processes used to obtain data that the evidence is safe to rely on. The latter requirement did not disappear in the wake of the repeal of section 69 Police and Criminal Evidence Act 1984. Nor did it disappear by the introduction of the Criminal Procedures and Investigations Act 1996, The Police Act 1997, The Regulation of Investigatory Powers Act 2000 and so on..
The purpose of raising this discussion (for examiners and students) about mobile phone forensic examination and tools it that discussions on these types of topics are not simply about providing answers and solutions to problems, but identifying potential questions that need to be adddressed before using cloned test SIM cards..Lastly, I have not described every event dealing with the examination of a dual SIM card mobile phone or how Samsung D880 manages the operation and functionality of both SIM cards. By not referring to these matters it has helped simplify and refine the discussion to keep the important points to the fore.











 .
.